Login Packet: Difference between revisions
(Add brief overview) |
(→Opcodes and packets: Add better explanation of patching packets) |
||
| (5 intermediate revisions by the same user not shown) | |||
| Line 16: | Line 16: | ||
[[Login_Packet_Results|Result values]] signal the result of server operations. | [[Login_Packet_Results|Result values]] signal the result of server operations. | ||
[[Login_Packet_Security_Flags|Security flags]] are used | [[Login_Packet_Security_Flags|Security flags]] are used {{Template:Sandbox/VersionRange|min_expansionlevel=2}}. | ||
= Overview = | = Overview = | ||
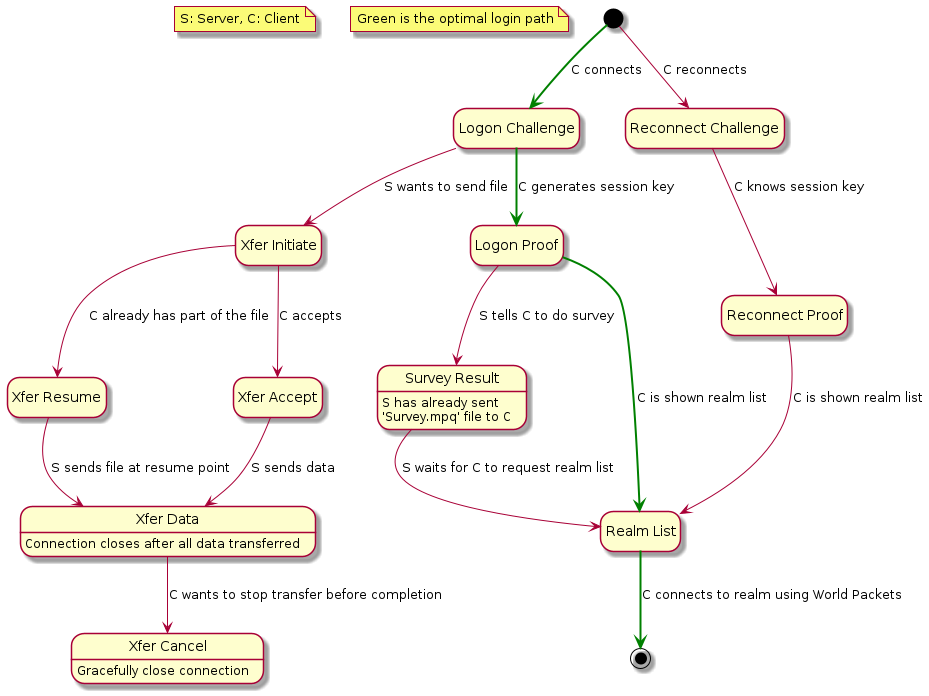
[[File:Login-packets-state-machine.png|400px|thumb|right|State machine diagram of the packets and where they fit into the login process. The optimal login path has been highlighted in green.]] | |||
The client initiates a TCP connection to the server on either the default port of 3724, or a port specified in the Realmlist.wtf file. | The client initiates a TCP connection to the server on either the default port of 3724, or a port specified in the Realmlist.wtf file. | ||
| Line 28: | Line 30: | ||
# Server performs calculations and returns a [[CMD_AUTH_LOGON_PROOF_Server]] with either a server proof or a [[Login_Packet_Results|failure code]] | # Server performs calculations and returns a [[CMD_AUTH_LOGON_PROOF_Server]] with either a server proof or a [[Login_Packet_Results|failure code]] | ||
# Client requests a realm list with [[CMD_REALM_LIST_Client]] and the server responds with [[CMD_REALM_LIST_Server]]. | # Client requests a realm list with [[CMD_REALM_LIST_Client]] and the server responds with [[CMD_REALM_LIST_Server]]. | ||
# Client selects a server and sends | # Client selects a server and opens a TCP connection to the Realm Server on either the default port of 8085, or the port specified in the realm list. The client keeps the connection alive to the authentication server. | ||
# Realm Server sends the [[SMSG_AUTH_CHALLENGE]] [[World Packet]] to the client and continues with realm server authentication. | |||
= Opcodes and packets = | = Opcodes and packets = | ||
| Line 52: | Line 55: | ||
!colspan="5"| Miscellaneous | !colspan="5"| Miscellaneous | ||
|- | |- | ||
| CMD_SURVEY_RESULT || 0x04 || Used for hardware survey. || [[CMD_SURVEY_RESULT_Client|Client]] || | | CMD_SURVEY_RESULT || 0x04 || Used for hardware survey. || [[CMD_SURVEY_RESULT_Client|Client]] || - | ||
|- | |- | ||
!colspan="5"| Realmlist | !colspan="5"| Realmlist | ||
| Line 60: | Line 63: | ||
!colspan="5"| Patching | !colspan="5"| Patching | ||
|- | |- | ||
| CMD_XFER_INITIATE || 0x30 || | | CMD_XFER_INITIATE || 0x30 || Sent by server when it wants to send data. || - || [[CMD_XFER_INITIATE_Server|Server]] | ||
|- | |- | ||
| CMD_XFER_DATA || 0x31 || | | CMD_XFER_DATA || 0x31 || Data sent by the server. || - || [[CMD_XFER_DATA_Server|Server]] | ||
|- | |- | ||
| CMD_XFER_ACCEPT || 0x32 || | | CMD_XFER_ACCEPT || 0x32 || Sent by client after getting an CMD_XFER_INITIATE from the server. || [[CMD_XFER_ACCEPT_Client|Client]] || - | ||
|- | |- | ||
| CMD_XFER_RESUME || 0x33 || | | CMD_XFER_RESUME || 0x33 || Sent by client that already has part of the data the server wants to send. || [[CMD_XFER_RESUME_Client|Client]] || - | ||
|- | |- | ||
| CMD_XFER_CANCEL || 0x34 || | | CMD_XFER_CANCEL || 0x34 || Sent by client that wishes to gracefully close the connection. || [[CMD_XFER_CANCEL_Client|Client]] || - | ||
|} | |} | ||
Latest revision as of 18:25, 4 June 2021
Login packets are packets sent by the client to the authentication server as the first connection to the server infrastructure.
All packets start with an opcode field but do not use the same values as the World Packets. The only packets that can start a connection are CMD_AUTH_LOGON_CHALLENGE Client and CMD_AUTH_RECONNECT_CHALLENGE Client which share packet layout.
There are minor differences in the packets between WoW versions, but the layout seems to be stable around ![]() and later.
and later.
The login packets are internally referred to as grunt and the packet layouts hint at it being planned for use for games other than WoW.
The client always sends the first packet in a category, and the server responds with a packet from the same category. So the client would send a CMD_AUTH_LOGON_CHALLENGE_Client and the server would respond with a CMD_AUTH_LOGON_CHALLENGE_Server.
The names here are used internally in the clients.
See Login for a higher level overview of the login process.
Result values signal the result of server operations.
Security flags are used ≥ ![]() .
.
Overview
The client initiates a TCP connection to the server on either the default port of 3724, or a port specified in the Realmlist.wtf file. The exchange is then:
- Client sends a CMD_AUTH_LOGON_CHALLENGE_Client containing the username and version information.
- Server responds with a CMD_AUTH_LOGON_CHALLENGE_Server containing either authentication values or a failure code.
- Client performs authentication calculations and sends a CMD_AUTH_LOGON_PROOF_Client.
- Server performs calculations and returns a CMD_AUTH_LOGON_PROOF_Server with either a server proof or a failure code
- Client requests a realm list with CMD_REALM_LIST_Client and the server responds with CMD_REALM_LIST_Server.
- Client selects a server and opens a TCP connection to the Realm Server on either the default port of 8085, or the port specified in the realm list. The client keeps the connection alive to the authentication server.
- Realm Server sends the SMSG_AUTH_CHALLENGE World Packet to the client and continues with realm server authentication.
Opcodes and packets
| Name | Value | Description | Client Link | Server Link |
|---|---|---|---|---|
| Authentication | ||||
| CMD_AUTH_LOGON_CHALLENGE | 0x00 | Intial information sent by client and then challenge by server. | Client | Server |
| CMD_AUTH_LOGON_PROOF | 0x01 | Proof sent by client and then server. | Client | Server |
| CMD_AUTH_RECONNECT_CHALLENGE | 0x02 | Reconnect challenge sent by client and then server. | Client | Server |
| CMD_AUTH_RECONNECT_PROOF | 0x03 | Reconnect proof sent by client and then server. | Client | Server |
| Miscellaneous | ||||
| CMD_SURVEY_RESULT | 0x04 | Used for hardware survey. | Client | - |
| Realmlist | ||||
| CMD_REALM_LIST | 0x10 | Realmlist request sent by client and realmlist information sent by server. | Client | Server |
| Patching | ||||
| CMD_XFER_INITIATE | 0x30 | Sent by server when it wants to send data. | - | Server |
| CMD_XFER_DATA | 0x31 | Data sent by the server. | - | Server |
| CMD_XFER_ACCEPT | 0x32 | Sent by client after getting an CMD_XFER_INITIATE from the server. | Client | - |
| CMD_XFER_RESUME | 0x33 | Sent by client that already has part of the data the server wants to send. | Client | - |
| CMD_XFER_CANCEL | 0x34 | Sent by client that wishes to gracefully close the connection. | Client | - |